- 7000 new cyber vulnerabilities were disclosed in Q1 of 2023.
- 56% of new vulnerabilities were exploited within 7 days of public disclosure
- And 32% of successful cyber intrusions start with the exploit of a vulnerability
A robust vulnerability management process is fundamental to improving cyber resilience. The best practice frameworks from Cyber Essentials to ISO27001 to NIST CSF and NCSC CAF all state the importance of vulnerability management, however the current landscape makes it a time consuming, challenging and never ending operational task. A crystal ball to show when and what the next 0-day looks like would be ideal, but the reality is, you simply have to be prepared and embrace a modern mind set and approach to best control the risk. With the sheer volume of new CVEs being continuously disclosed and speed at which attackers are exploiting them, it’s not possible to mitigate every vulnerability which is why risk based prioritisation and automated remediation will become the norm.
There’s some way to go according to the 2023 UK Gov Cyber Breach Survey. Only 31% of businesses have a policy to apply software security updates within 14 days and only 34% have technical rules and controls in place for patch management!
Unfortunately no magic hands off solution exists to fix all vulnerabilities, however there is process and technology that significantly reduces the amount of operational effort to keep on top of the challenge and remediate risk efficiently to keep ahead of the attackers. By implementing the right tools with sensible automation, ultimately risk is reduced faster meaning less time spent reactively remediating and more time to focus on driving the security plan forward.
Process: Continuously identify where your vulnerabilities exist, use risk based prioritisation to focus remediation efforts, apply fixes quickly and use automation where possible to increase volume.
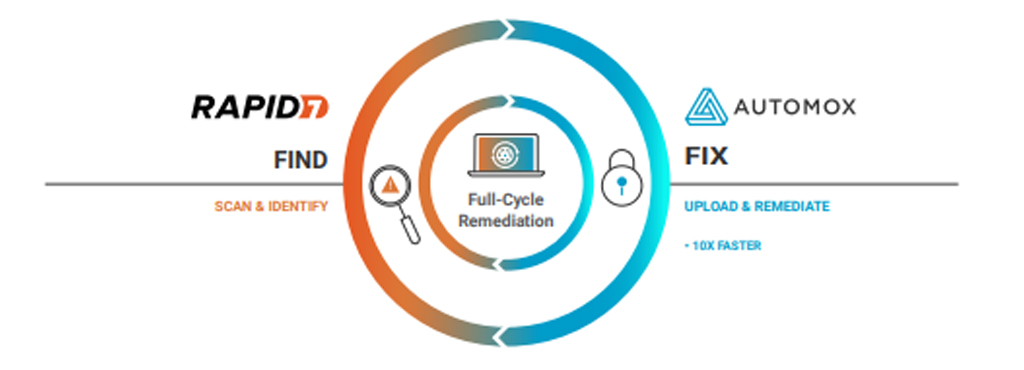
Technologies: If you implement the right tools with sensible automation, ultimately risk is reduced faster. Rapid7 IVM and Automox are Saepio’s tools of choice after extensive research into the market. They are a fantastic pairing, joining forces to enable full-cycle vulnerability management by automating the manual tasks in traditional patching and remediation routines.
With Rapid7 continuously finding vulnerabilities in your environment and fuelling Automox with prioritised information to trigger automated patching, the volume and speed of vulnerability remediation is increased which in turn helps hit the best practice recommendations.
A final note, it’s recommended to have emergency patching procedures and incident response playbooks in place so that in the event of a widespread threat or breach, your team has a well-understood mechanism to drive immediate action.
As always, we’re on hand to talk more and answer questions!
Contact Us
If you’d like to talk further about any of the issues raised in this blog, then please do reach out to the Solutions Team at Saepio on contact@saepio.co.uk.